Unicast peers are not supported in strict mode
Error reporting information, reasons for error reporting, and exclusion of error digressions
Error message
Oct 14 19:18:45 ka1 Keepalived_vrrp[1306]: (Web_1) Strict mode does not support authentication. Ignoring.
Oct 14 19:18:45 ka1 Keepalived_vrrp[1306]: (Web_1) Unicast peers are not supported in strict mode
Oct 14 19:18:45 ka1 Keepalived_vrrp[1306]: Stopped - used 0.000000 user time, 0.001451 system time
Oct 14 19:18:45 ka1 Keepalived[1305]: Startup complete
Oct 14 19:18:45 ka1 Keepalived[1305]: pid 1306 exited with permanent error CONFIG. Terminating
Oct 14 19:18:45 ka1 Keepalived[1305]: CPU usage (self/children) user: 0.000000/0.000000 system: 0.001419/0.001747
Oct 14 19:18:45 ka1 Keepalived[1305]: Stopped Keepalived v2.2.4 (08/21,2021)
Error reporting reason
vrrp_Strict mode and unicast_src_IP conflicts cause keepalived startup failure
in addition, VRRP_Strict also conflicts with nopreempt and other configurations. It is recommended to delete or comment directly
Troubleshooting errors
vi /etc/keepalived/keepalived.conf
Comment or delete the following lines
#vrrp_strict
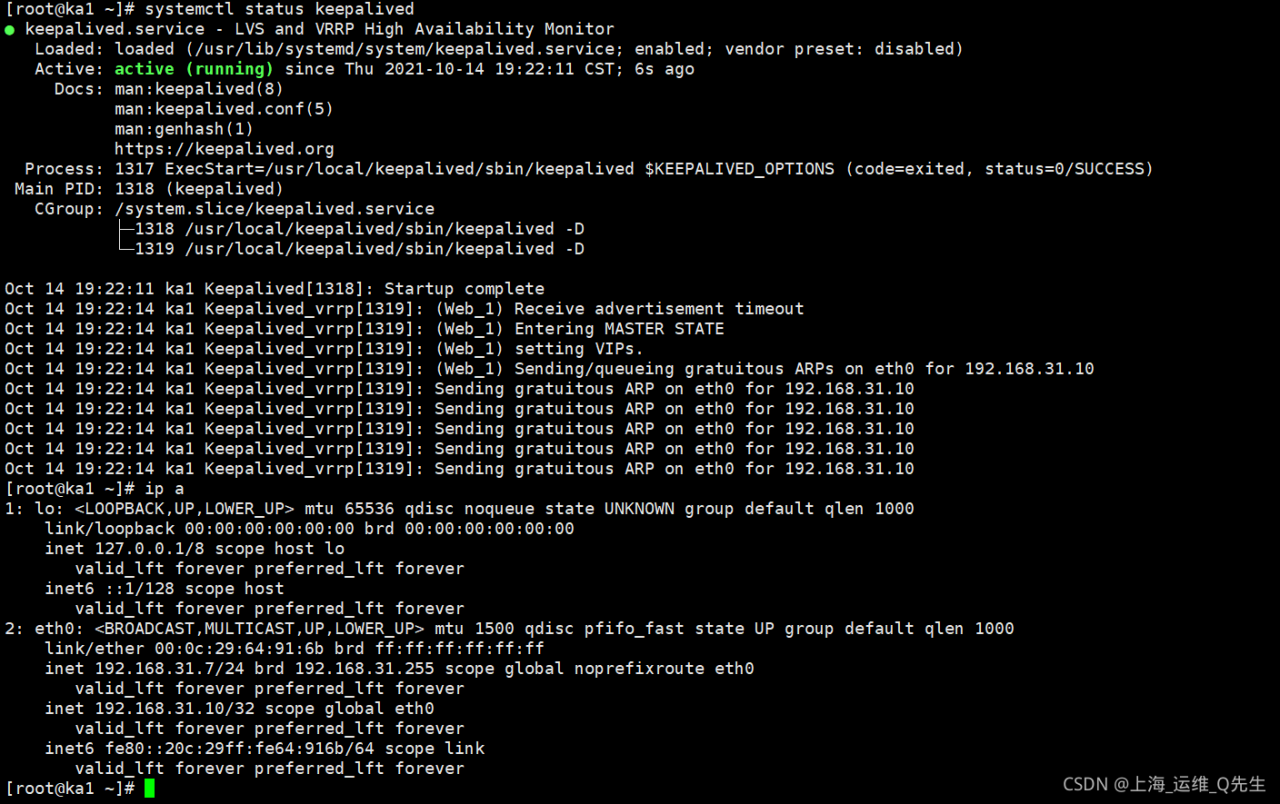
Restart keepalived after saving
systemctl restart keepalived
Digression
See other students’ keepalived help posts during troubleshooting
https://ask.csdn.net/questions/771124?Wechatoa =
although we don’t know the final reason, we also analyze the problem
The problem is divided into two steps
first, the automatic switching of VIP caused by preemption is mainly
1.43. When 43 is started, the virtual IP is switched to 43, which is caused by preemption mode.
solution: set keepalived to non gunfight mode, so that you stop 43, switch to 47, and start 43 again without forcing the VIP to switch back to 43.
VRRP_ Nopreempt
II. VIP is inaccessible on 43.
VIP is inaccessible. The specific phenomenon of “inaccessibility” described here is not well understood. It is speculated that there are three possibilities.
1vip cannot Ping through
look at the firewall configuration
systemctl stop firewalld & amp& amp; Iptables – f (please confirm the firewall configuration again and again to avoid losing some required configurations)
for the configuration of keepalived, theoretically you do not configure VRRP_ Strict is VRRP that does not need to be configured separately_ Iptables, but you didn’t mention the specific keepalived version. It doesn’t rule out some special bugs in the small version
Global_ Adding VRRP to defs_ Iptables
3. A service such as nginx or Apache cannot be accessed
3.1. Check the listen configuration item of the corresponding configuration file. The most brutal way is to set it to 0.0.0
3.2. SS – ntlp to check the listening of the corresponding port
3.3. Use tools such as curl to test 127.0.0.1 successively, server IP and VIP to see whether they return normally.
3.4. If the database is used, check the authorization of relevant accounts
Read More:
- [Solved] Linux Compile Error: error: ‘for’ loop initial declarations are only allowed in C99 mode
- [Solved] SSH Error: ECDSA host key for xxx has changed and you have requested strict checking.
- Prompt “entering emergency mode. Exit the shell to continue” if the Linux operating system does not start normally
- RuntimeError: 0:1 (10): error: GLSL 3.30 is not supported. [How to Solve]
- Linux yum Error: All mirror URLs are not using ftp
- [Solved] Error (suppressible): (vsim-12110) All optimizations are disabled because the -novopt option is in effect…
- CentOS/RHEL 7: How to Reinstall GRUB2 from Rescue Mode (EFI)
- Centos7 Start Error: Entering emergency mode.Exit the shell to continue
- [Solved] Virtual Machine Centos7 Startup Error: Entering emergency mode
- Solution of device eth0 does not see to be present, delaying initialization. Error in network card under Linux
- [Solved] Raspberry Pi Error: VNC error “No configured security type is supported by 3.3 VNC Viewer“
- SSH Connect Service Error: Could not connect to ‘xxx.xxx.xx.xx‘ (port 22): Connection failed.
- [Solved] Git Clone Failed Error: 4069 bytes of body are still expected
- [Solved] zookeeper Cluster error: Error: JAVA_HOME is not set and java could not be found in PATH.
- [Solved] Linux — 9 — txt files are copied from windows to Linux and read error
- [Solved] websocket: the client is not using the websocket protocol: ‘upgrade’ token not found in ‘Connection’ head
- [Solved] UnicodeEncodeError: ‘ascii‘ codec can‘t encode characters in position 3-9: ordinal not in range(128)
- [Solved] error: ‘QStringLiteral’ was not declared in this scope
- [Solved] Nginx Startup Error: directive is not allowed here in
- [Solved] websocket error in Linux service: / lib64 / libc. So. 6: version ` glibc_2.17‘ not found